
The US government issued emergency legislation on Sunday after the largest fuel pipeline in the US was hit by a ransomware cyber-attack.
The Colonial Pipeline carries 2.5 million barrels a day - 45% of the East Coast's supply of diesel, gasoline and jet fuel.
It was completely knocked offline by a cyber-criminal gang on Friday and work to restore service is continuing.
The emergency status relaxes rules on fuel being transported by road.
It means drivers in 18 states can work extra or more flexible hours when transporting refined petroleum products.
US fuel prices at the pump were largely unaffected on Monday, but experts say that could change if the shutdown is prolonged.
Independent oil market analyst Gaurav Sharma told the BBC a lot of fuel was now stranded at refineries in Texas.
"Unless they sort it out by Tuesday, they're in big trouble," said Mr Sharma. "The first areas to be impacted would be Atlanta and Tennessee, then the domino effect goes up to New York."
He said oil futures traders were now "scrambling" to meet demand, at a time when US inventories are declining, and demand - especially for fuel for cars - is on the rise as consumers return to the roads and the economy recovers.

The temporary waiver issued by the Department of Transportation enables oil products to be shipped in tankers up to New York, but this would not be anywhere near enough to match the pipeline's capacity, Mr Sharma warned.
Multiple sources have confirmed that the ransomware attack was caused by a cyber-criminal gang called DarkSide, who infiltrated Colonial's network on Thursday and took almost 100GB of data hostage.
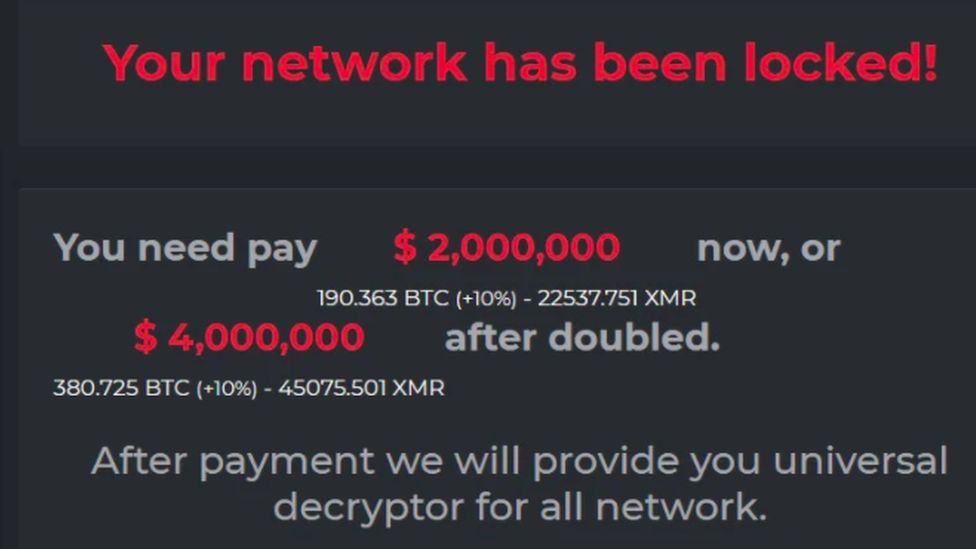
After seizing the data, the hackers locked the data on some computers and servers, demanding a ransom on Friday. If it is not paid, they are threatening to leak it onto the internet.
Colonial said it was working with law enforcement, cyber-security experts and the Department of Energy to restore service.
On Sunday, it said that although its four main lines remain offline, some smaller lateral lines between terminals and delivery points were now operational.
"Quickly after learning of the attack, Colonial proactively took certain systems offline to contain the threat. These actions temporarily halted all pipeline operations and affected some of our IT systems, which we are actively in the process of restoring," the firm said.
It added it would bring its full system back online "only when we believe it is safe to do so, and in full compliance with the approval of all federal regulations".
Ransomware as a service
The incident highlights the increasing risk ransomware is posing to critical national industrial infrastructure, not just businesses.
It also marks the rise of a criminal IT eco-system worth tens of millions of pounds, that is unlike anything the cyber-security industry has ever seen before.
In addition to a notice on their computer screens, victims of a DarkSide attack receive an information pack informing them that their computers and servers are encrypted.
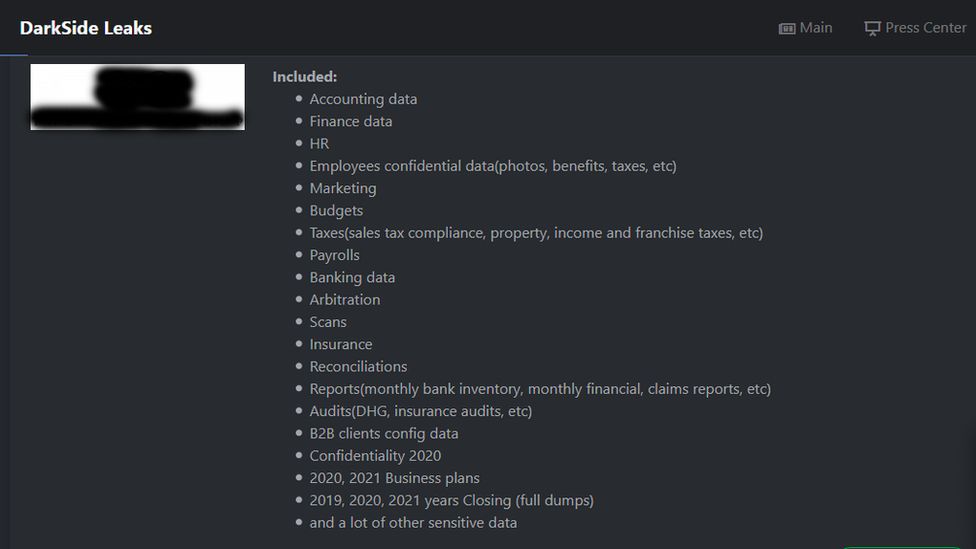
The gang lists all the types of data it has stolen, and sends victims the URL of a "personal leak page" where the data is already loaded, waiting to be automatically published, should the company or organisation not pay before the deadline is up.
DarkSide also tells victims it will provide proof of the data it has obtained, and is prepared to delete all of it from the victim's network.
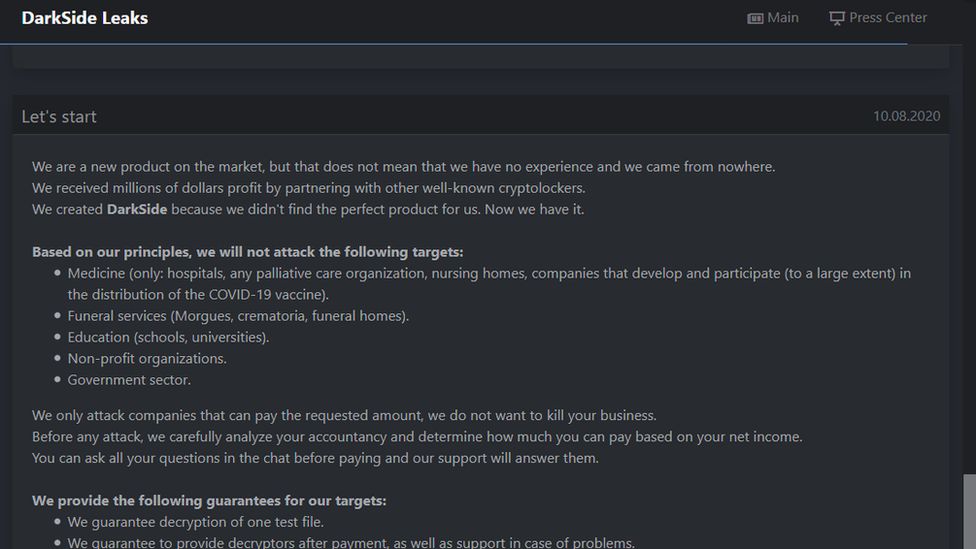
According to Digital Shadows, a London-based cyber-security firm, DarkSide operates like a business.
The gang develops the software used to encrypt and steal data, then trains up "affiliates", who receive a toolkit containing the software, a template ransomware demand email, and training on how to carry out attacks.
The affiliate cyber-criminals then pay DarkSide a percentage of their earnings from any successful ransomware attacks.
When it released new software in March that could encrypt data faster than before, the gang issued a press release and invited journalists to interview it.
It even has a website on the dark web where it lists all the companies it has hacked and what was stolen, and an "ethics" page where it says which organisations it will not attack.
How did the attack occur?
Cyber-security firm Digital Shadows says the Colonial attack has come about due to the pandemic - with more engineers remotely accessing control systems for the pipeline from home.
James Chappell, co-founder of Digital Shadows, believes DarkSide bought account login details relating to remote desktop software such as TeamViewer and Microsoft Remote Desktop.
"We're seeing a lot of victims now, this is seriously a big problem now," said Mr Chappell.
"The amount of small businesses that are falling victim to this - it's becoming a big problem for the economy globally."
Digital Shadows' research shows the cyber-criminal gang is likely to be based in a Russian-speaking country, as it avoids attacking companies in post-Soviet states including Russia, Ukraine, Belarus, Georgia, Armenia, Moldova, Azerbaijan, Kazakhstan, Kyrgyzstan, Tajikistan, Turkmenistan and Uzbekistan.
https://news.google.com/__i/rss/rd/articles/CBMiKmh0dHBzOi8vd3d3LmJiYy5jb20vbmV3cy9idXNpbmVzcy01NzA1MDY5MNIBLmh0dHBzOi8vd3d3LmJiYy5jb20vbmV3cy9idXNpbmVzcy01NzA1MDY5MC5hbXA?oc=5
2021-05-10 10:08:14Z
52781577598910
Tidak ada komentar:
Posting Komentar